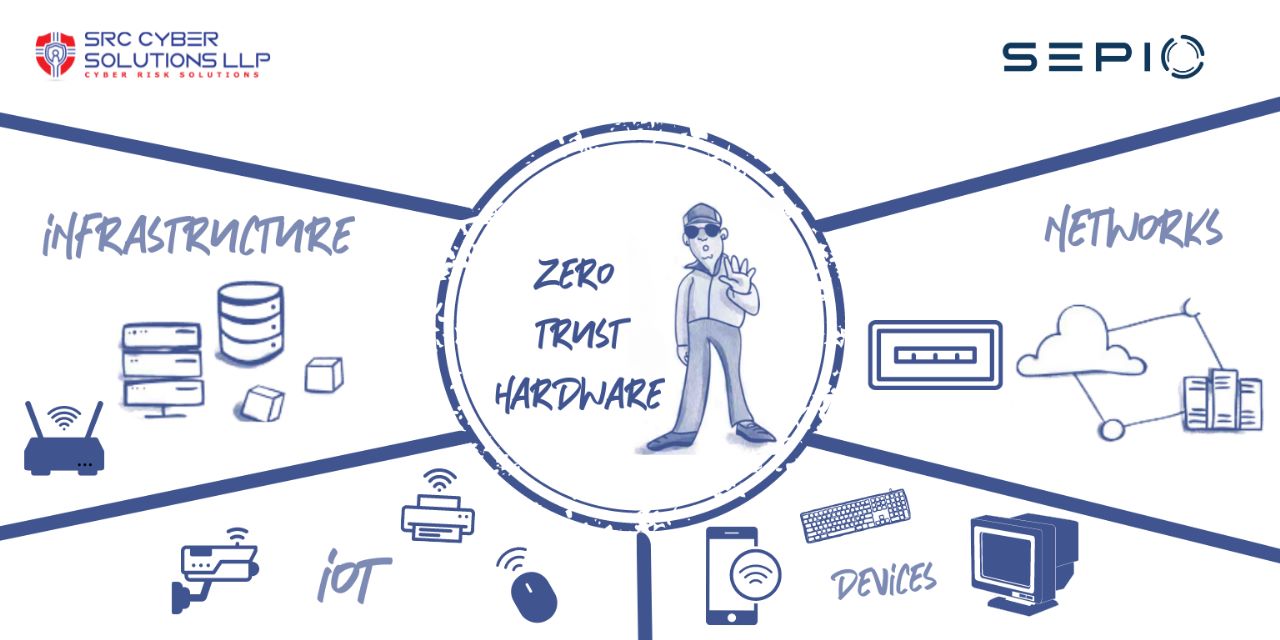
Embracing a Zero Trust Hardware Access Security Model
Embracing a Zero Trust Hardware Access Security Model is key. The concept of Zero Trust (ZT) is primarily a security model but also a mindset. ZT is based on the idea that threat exists everywhere, both inside and outside traditional network boundaries. Essentially, anyone and anything can be a security risk. Hence, by assuming that a breach is inevitable, ZT eliminates the automatic trust given to enterprise users and devices. Instead, users’ and devices’ access to an enterprise’s resources is based on a dynamic policy that attempts to reduce the attack surface by providing access based on the principle-of-least-privileged (PLP). PLP is applied for every access decision, and access is constantly under review, requiring continuous verification through real-time information from various sources that detect anomalies and suspicious activities.
ZT is a data-based security model that relies on different sources of input to make real-time access decisions. In doing so, ZT aims to increase the enterprise’s security posture by improving its ability to address the existing threats. Transitioning to a ZTA is a complex process that requires planning and patience. For optimum efficacy, ZT must be included in most, if not all, aspects of the enterprise’s network and have the support of the entire organization, from c-level executives to entry-level employees and everything in between.
Today’s threat landscape is desperate for Zero Trust
As the world becomes increasingly connected, it also becomes less secure. Today, enterprises benefit from a wealth of devices that assist in operational capabilities. However, while this benefits the enterprise, it also benefits attackers seeking to exploit such devices. The volume of data possessed by organizations has grown exponentially to enable connectivity and has done so in an increasingly mobile environment. Hence, data is no longer tied to a specific location, and it is both endpoints and networks which facilitate remote data access. Endpoints make attractive targets not only because of the data stored on them, but also the network access that they can provide an attacker with. This includes IoT devices which are often used as an attack vector. According to a 2020 report on Zero Trust Endpoint and IoT Security by Cybersecurity Insiders, there is a concern among 61% of organizations regarding endpoints and IoT devices gaining insecure network access and remote access.
Even more worrisome is that attackers’ tactics, techniques, and procedures (TTP) improve as security solutions become stronger. Malicious actors are finding increasingly innovative and deceptive ways to exploit the blind spots that security solutions do not cover. 40% of organizations claim that they have insufficient protection against the newest threats, according to the Cybersecurity Insiders report. Traditional perimeter-based network and endpoint detection and response solutions prove ineffective as cybercriminals have repeatedly demonstrated their ability to bypass many of these defense measures.
Malicious actors exploit the trust given to internal users and devices, resulting in successful attacks. By removing the concept of trust, ZT minimizes organizations’ susceptibility to network infiltration stemming from unauthorized devices and their users.
Zero Trust
While it is still necessary for enterprises to implement traditional security solutions as a form of tactical response, ZT provides a strategic framework that enables a shift to proactive security. As such, organizations can benefit from a hybrid environment that is both proactive and reactive, thus increasing the overall cybersecurity posture. With ZT, the concept of trust is eliminated from the organization’s network architecture, thus providing more opportunities to identify threats and take subsequent action to avoid an attack. Importantly, ZT protects the enterprise outside its typical perimeters, which is especially relevant as telework, Bring Your Own Device (BYOD), and Internet of Things (IoT) devices become increasingly common “within” organizations. The ZT model ensures that network access is granted based on who, what, when, where, and how. However, to answer such questions, the enterprise must have complete device visibility.