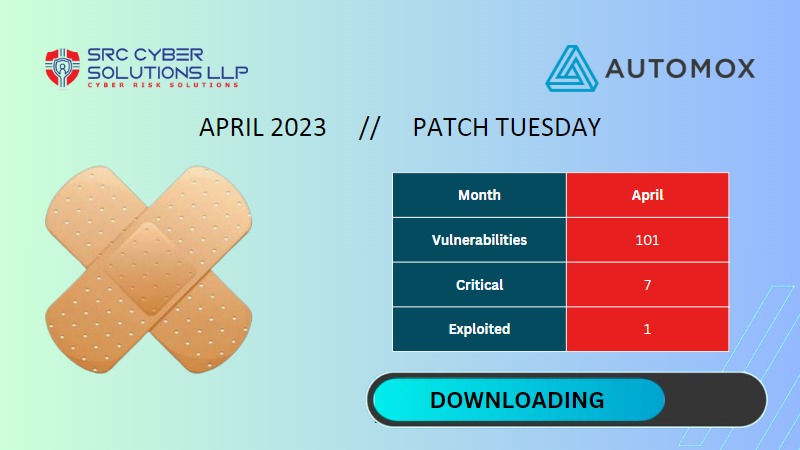
April Sees a Whopping 101 Vulnerabilities Patched
Experts Weigh in on April 2023 Patch Tuesday Release
April’s Patch Tuesday release from Microsoft sees an additional zero-day fixed and a total of 101 vulnerabilities patched, 7 of them critical. The zero-day is a flaw in the Windows Common Log File System (CLFS) that allows elevation to SYSTEM privileges. This is the most vulnerabilities patched since August of 2022 in what will be a heavy month for administrators.
While zero-days usually get the headlines, this month’s release has a few critical vulnerabilities that shouldn’t be overlooked by administrators. The first is a critical CVSS 9.8/10 remote code execution vulnerability in Microsoft Message Queuing that affects Windows 10, 11, and Server 2008-2022. It’s likely to be exploited and should be patched within 24 hours on endpoints exposed to the internet.
The other high-priority vulnerability is a CVSS score 8.8/10 in the Dynamic Host Configuration Protocol (DHCP) Server Service that allows an attacker with access to the restricted network to remotely execute code on the server. DHCP manages a record of all IP addresses, so attackers with access could deny service or direct DHCP clients to a malicious router. This vulnerability is likely to be targeted and exploited by attackers, and we recommend patching ASAP – ideally within 24 hours – as the impact of exploitation could be catastrophic.
Microsoft Patch Tuesday Vulnerabilities: A Brief History
CVE-2023-28252
Windows Common Log File System Driver Elevation of Privilege Vulnerability [IMPORTANT ZERO-DAY]
This same-named vulnerability was highlighted in the February Patch Tuesday and has been elevated from IMPORTANT to IMPORTANT ZERO-DAY for this month’s Patch Tuesday. The Windows Common Log File System (CLFS) Driver Elevation of Privilege once again impacts versions of Windows 10, Windows 11 as well as Windows Server 2008, 2012, 2016, 2019, and 2022 with no change from the previous base score metrics (low attack complexity, low privileges required, and no user interaction needed).
This vulnerability leverages existing system access to actively exploit a device and is a result of how the CLFS driver interacts with objects in memory on a system. To exploit this vulnerability successfully, a bad actor would need to log in and then execute a maliciously crafted binary to elevate the privilege level. An attacker who successfully exploited this vulnerability could then gain system privileges.
With an official fix from Microsoft, Automox recommends patch deployment within 24 hours since this is an actively exploited zero-day. - Gina Geisel
CVE-2023-21554
Microsoft Message Queuing Remote Code Execution Vulnerability [CRITICAL]
There is a critical, CVSS score 9.8/10 vulnerability in Microsoft Message Queuing that allows attackers to send a specially crafted MSMQ packet to an MSMQ server and remotely execute code on the server. To be vulnerable, Windows 10, 11, and Server 2008-2022 systems need to have the Windows message queuing server enabled on a system. Admins can check for a service named “Message Queuing” by listening on TCP port 1801 to see if the service is enabled.
Microsoft has released patches for Windows 10, 11, and Server 2008-2022 that administrators should apply ASAP on systems with the Message Queuing service enabled as Microsoft notes this vulnerability is more likely to be exploited by threat actors. - Peter Pflaster
CVE-2023-28231
DHCP Server Service Remote Code Execution Vulnerability [CRITICAL]
With low attack complexity and no user interaction required, the DHCP Server Service Remote Code Execution Vulnerability has been identified as a critical vulnerability impacting versions of Windows Server 2008, 2012, 2016, 2019, and 2022.
This vulnerability leverages the DHCP, a client/server protocol that automatically provides an IP host with its IP address and other related configuration information such as the subnet mask and default gateway. As an “adjacent” attack vector, successful exploitation of this vulnerability initially requires an attacker to gain access to the restricted network before running an attack. Once infiltrated, an authenticated attacker could then leverage a specially crafted remote procedure call (RPC) to the DHCP service to exploit this vulnerability. RPC is a communication protocol that a client can use to request a service from a server without having to understand the network's details.
Automox recommends deploying this fix across your impacted endpoints within 24 hours since the exploitation of your DHCP server could have a catastrophic impact on your organization, such as denial of service or directing DHCP clients to a malicious router. - Preetham Gurram
CVE-2023-28227
Windows Bluetooth Driver Remote Code Execution Vulnerability [IMPORTANT]
There is an important CVSS score 7.5/10 vulnerability in the Windows Bluetooth Driver that allows an attacker to remotely execute code on vulnerable devices. Attackers close to vulnerable systems can leverage a complex attack to send and receive radio transmissions from Windows 10, 11, and Server 2008-2022 endpoints to remotely execute code.
Bluetooth has been a targeted attack vector in the past, and Microsoft notes that this vulnerability is more likely to be exploited, though exploitation has not yet been detected in the wild. Due to the potential impact of remote code execution, we recommend patching within 72 hours on affected endpoints, especially remote ones. - Gina Geisel
