Financial Services and Supply Chain Attacks
Financial Services and Supply Chain Attacks
Download White PaperIn an ever-evolving digital landscape, businesses face countless challenges, from securing data to optimizing operations. We help you navigate these hurdles with confidence.
Many organizations struggle to gain complete visibility of their assets, leading to blind spots in security and operations.
Identifying and mitigating risks across dynamic infrastructures is a constant challenge for modern businesses.
Managing data flows between third-party integrations while ensuring security and compliance is increasingly complex.
Keeping up with changing regulations such as GDPR, HIPAA, and PCI-DSS can be overwhelming without the right tools.
Migrating to and managing cloud infrastructure introduces complexities that many teams are unprepared to handle.
Businesses face a rise in sophisticated cyber threats that require proactive monitoring and defenses.

Managing third-party data flows can be a daunting task, with risks of data leaks and compliance issues. Our advanced solution empowers organizations to secure and optimize third-party integrations while maintaining data integrity and compliance.
Gain complete visibility into third-party data transactions and monitor data flow in real-time to detect anomalies and prevent leaks.
Ensure compliance with GDPR, HIPAA, and other regulations by automating data redaction, encryption, and secure transfers.
We deliver unparalleled visibility and control over third-party data interactions, enabling your organization to mitigate risks, ensure compliance, and streamline secure integrations.
Ready to transform your approach to data security? Let's connect.
Explore our detailed case studies to see how organizations have enhanced security, ensured compliance, and optimized third-party data flows with our innovative solutions.

SRC SRC Supply Chain Governance 1 Executive Summary...
View Case Study →
SRC Securing your Data Supply Chain ...
View Case Study →
SRC How CMMC and the Digital Supply Chain Security...
View Case Study →Explore our white papers to gain knowledge about managing third-party data flows securely, ensuring compliance, and mitigating risks associated with sensitive data.
Financial Services and Supply Chain Attacks
Download White PaperWatch our videos to discover strategies for managing third-party data securely, automating sensitive data redaction, and ensuring compliance in real time.





Stay ahead with expert insights, actionable strategies, and the latest advancements in third-party data flow management. Learn how to enhance security, ensure compliance, and streamline data exchanges with confidence.

Discover how SRC’s third-party data flow management system delivers real-time visibility, control, and risk reduction. Streamline compliance, prevent data leaks, and secure your use of AI tool, without the jargon.
Read Blog
This blog explains what data catalogs are and why they are an important investment
Read Blog
Open source security is a term used to describe the process of protecting your organization’s data and network from attack by using open-source software. It refers to the use of open-source software (OSS) for data protection. Open source software is free to use, meaning that anyone can access it wit
Read Blog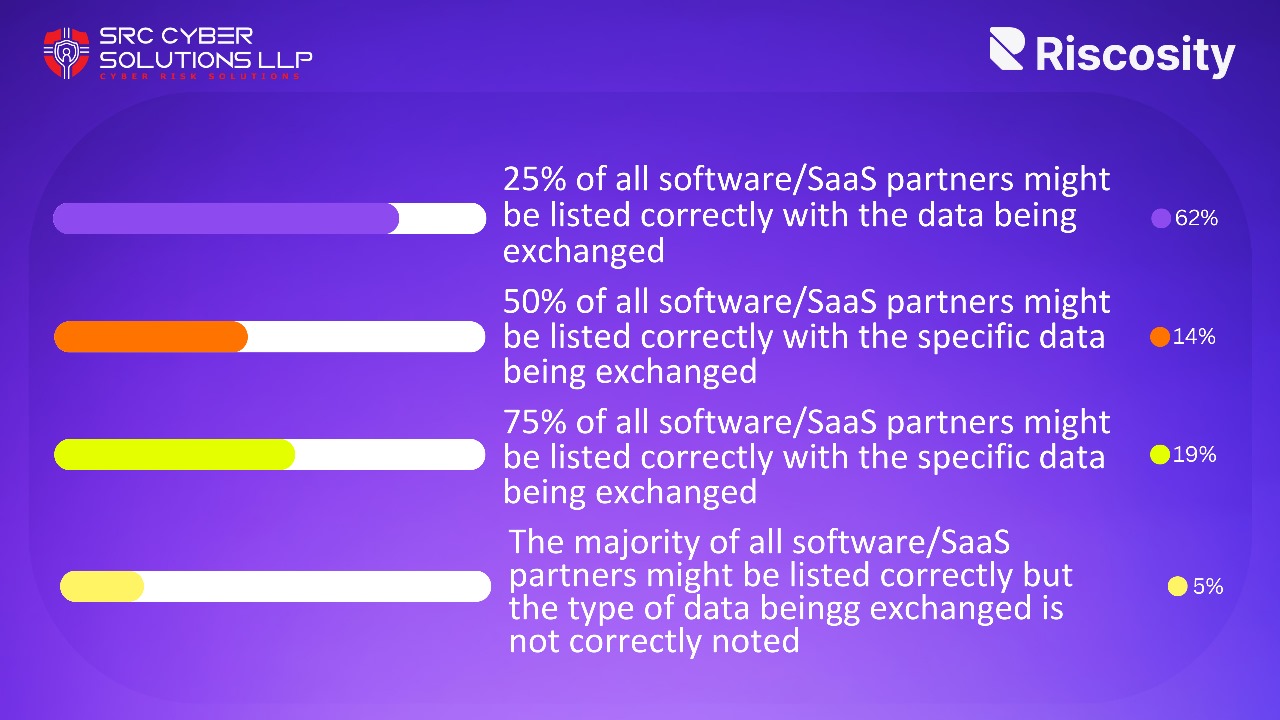
Keeping a Pulse on All Third-Party Connections One of the main goals of information security is to protect assets. Security Guest Expert Security Expert Published on 1/17/2024 5min. A blog image for the how to respond to the MOVEit attack blog. The core tenets of information security i
Read Blog
A comprehensive application risk assessment guide sharing tips and considerations of the process of evaluating and understanding the security risks associated with an application.
Read Blog
Data lineage and data provenance are related terms, but different. Lineage focuses on the origins and movements of data over time, while provenance focuses on the transformations and derivations of data from original sources. Provenance helps teams to follow the source of data and verify its authent
Read Blog
105 Naurang House
21 Kasturba Gandhi Marg
Connaught Place
New Delhi - 110 001 INDIA
+91 120 2320960 / 1
sales@srccybersolutions.com
Reach out to the world’s most reliable IT services.
Dive into our diverse range of services designed to secure, streamline, and transform your business operations. From advanced endpoint management to strategic IT consulting, we’re here to support your growth journey.
Take control of your endpoint security in cyber security with our automated patch solution. Streamline system updates, patch management, and endpoint protection across your entire network. Reduce security gaps and human error while ensuring all your devices stay protected and compliant.
Know MoreGuard against sophisticated email threats with our AI-powered protection system. From phishing attempts to business email compromise, our solution detects and neutralizes email security threats in real-time. Our comprehensive email security solution provides multi-layered defense against evolving digital risks.
Know MoreBuild a stronger security culture through comprehensive cyber security training programs. Our hands-on approach ensures your team understands modern cyber threats and best practices for protection. Transform your employees into your first line of defense against digital attacks.
Know MoreImplement automated microsegmentation without complex agent deployments. Create secure zones in your network to contain and control potential threats. Protect critical assets while maintaining operational flexibility through intelligent network segmentation.
Know MoreWe protect the things that matter most to our customers by pushing the boundaries of cybersecurity. Over the decades, we've hustled and innovated, we've grown and transformed, to create the world's most advanced cybersecurity platform.
Know More